Lab 2: Using TShark
Objective
To install and use TShark, which is a terminal packet sniffer, and explore packets being processed by a machine as it's running.
Installation
Wireshark is a popular packet sniffer/analyzer. We will be using the terminal version of this program which is called TShark. First you need to install the tshark package, which can be done as follows:
ifinlay@vm:~$ sudo apt install tshark
Then enter 'y' when it asks if you want to continue. It will then ask if non-superusers should be able to capture packets. You should answer yes to this question as well.
You must then add your current user to the wireshark group so that you have access to the network. That can be done with this command:
ifinlay@vm:~$ sudo usermod -a -G wireshark $USER
You must then logout of your virtual machine, and log back in again.
If you get the following error message:
ifinlay@tester:~$ tshark Capturing on 'Cisco remote capture' tshark: Couldn't run /usr/bin/dumpcap in child process: Permission denied tshark: Error by extcap pipe: ** (process:3997): WARNING **: 02:15:33.585: Missing parameter: --remote-host 0 packets captured
Then you did not setup the group properly.
Using TShark
When you run the command tshark command, it will print all of the
packets being processed by the machine. Below is an example:
ifinlay@vm:~$ tshark
Capturing on 'ens4'
1 0.000000000 10.142.0.3 → 173.71.207.247 SSH 102 Server: Encrypted packet (len=36)
2 0.013974434 173.71.207.247 → 10.142.0.3 TCP 66 44260 → 22 [ACK] Seq=1 Ack=1 Win=323 Len=0 TSval=913110574 TSecr=3780862521
3 0.014002333 173.71.207.247 → 10.142.0.3 TCP 66 44260 → 22 [ACK] Seq=1 Ack=37 Win=323 Len=0 TSval=913110575 TSecr=3780862523
4 0.023856025 173.71.207.247 → 10.142.0.3 TCP 78 [TCP Dup ACK 3#1] 44260 → 22 [ACK] Seq=1 Ack=37 Win=323 Len=0 TSval=913110581 TSecr=3780862608 SLE=1 SRE=37
5 0.431006150 10.142.0.3 → 173.71.207.247 SSH 198 Server: Encrypted packet (len=132)
6 0.431048991 10.142.0.3 → 173.71.207.247 SSH 102 Server: Encrypted packet (len=36)
7 0.431140897 10.142.0.3 → 173.71.207.247 SSH 238 Server: Encrypted packet (len=172)
You will need to type Ctrl-C to stop tshark when you are done. The columns displayed by default are:
- An index number which just starts at 1 and increments.
- The number of seconds since tshark was started that the packet was processed.
- The source and destination address of the packets. The source is on the left and the destination on the right. Here 10.142.0.3 is the internal IP address of my VM, and 173.71.207.247 is the external IP of my home router. The only traffic at this point is between these two machines.
- The protocol. Here there are two protocols, SSH and TCP.
- The number of bytes in the packet.
- Information about what's in the packet. SSH packets are encrypted, so tshark just says that. The "ACK" packets stand for "acknowledgement". Part of the TCP protocol is that when packets are received, a small "ACK" packet is sent back to the sender so it knows it went through. SSH is an application layer protocol built on top of TCP, which is at the transport layer. Those ACKs are my machine sending the VM acknowledgement that it received SSH packets.
Instead of tshark running indefinitely, we can tell it to read some number of packets and stop with the -c flag (which stands for count):
ifinlay@vm:~$ tshark -c 10
We can also have tshark dump the data into a file rather than directly to the screen with the -w flag (which stands for write):
ifinlay@vm:~$ tshark -c 10 -w traffic.pcap
This way the data can be stored for later analysis or backup. The .pcap extension stands for "packet capture" and is a standard format for information on network packets. It is not a human-readable format, but stores all the information tshark can get from the packets including the actual contents.
To have tshark print its information on a .pcap file, we can give it the -r flag, which stands for read:
ifinlay@vm:~$ tshark -r traffic.pcap
Analysing an Application
For this lab, we will analyze packets sent as part of the HTTP web protocol. To start off, install the Apache web server on your VM with the following command:
ifinlay@vm:~$ sudo apt install apache2
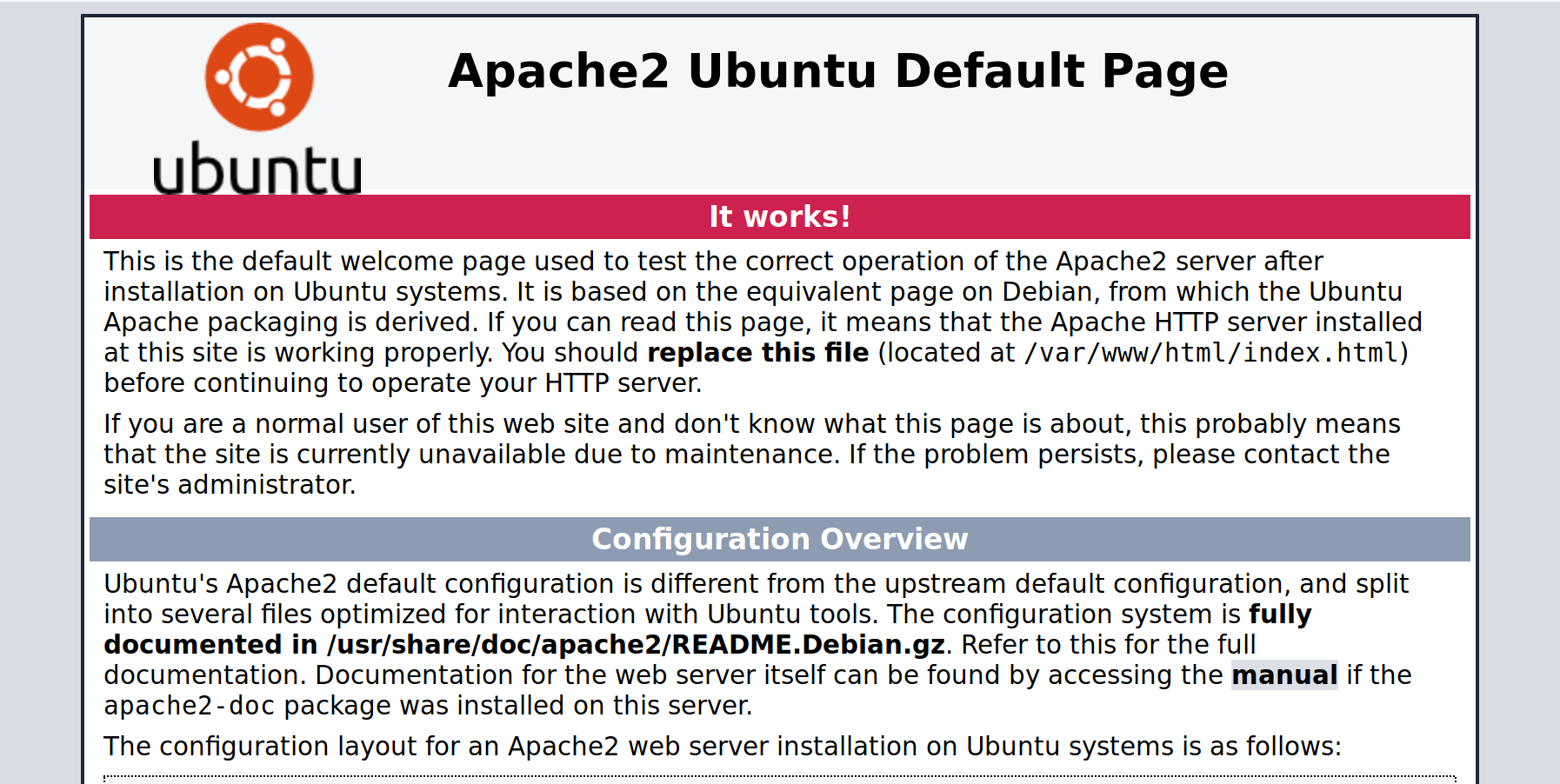
Hit 'y' when it asks you to confirm. To test that the web server is working, navigate to your VM's IP address from a web browser. You should see the default web page, the top of which looks like this:
If we want to show packets from one particular application, without all the noise from our SSH connection, we can do it with the -f, "filter" argument to tshark.
These can be used to only view traffic that we are interested in, such as only from a specific host, or on a specific port. HTTP uses port 80, so if we want to see only HTTP traffic, we can do it like so:
ifinlay@vm:~$ tshark -f "port 80"
Now only packets for the HTTP server will be displayed instead of all network traffic. You will use tshark to view HTTP packets for the rest of this lab.
Questions
For this lab, use tshark to answer the following questions about HTTP. You can do this in the body of an email, or as a separate document.
- Open up your VM's default web site in a browser again (or refresh it if you still have it open). How many packets are sent in total between the two machines to do this?
- How much time does it take to complete the process?
- How many of these packets are from the VM to your browser, and how many from the browser to the VM?
- One of the packets from your browser to the VM is different than the others. What do you think it's doing?
- Why are the smallest packets all the same size? What do they contain?
- Which of these packets has the greatest size? What data do you think that packet contains?
- Do this experiment again, but now instead of just putting your VM's IP address into the URL bar of your browser, append "/missing.html" instead. The browser should show a "Not Found" message. What is different in the packets that are produced by doing this? Be as detailed as you can.
Submitting
When you're finished, email your answers to ifinlay@umw.edu.